This short article looks at the behavior of the BGP Backdoor Route feature. Although this has been explained, both in books and in other articles on the net, I would like to make a few points that I feel are not covered properly. Skip to the end if you are already familiar with the feature, as the first part provides a quick refresher.
The Setup
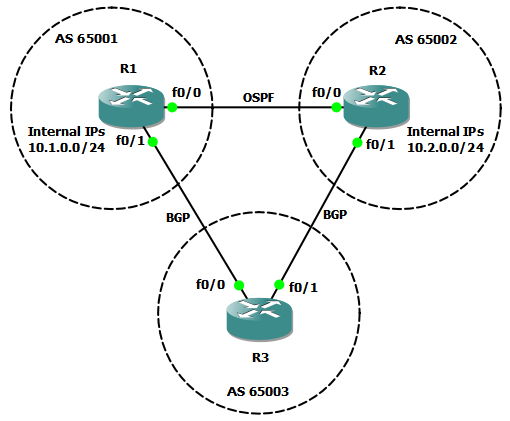
The topology is rather trivial to build and configure so I will not walk you through that. R1 and R2 are running OSPF between them and each router is in its own AS for the purposes of running eBGP between all of them. In this example, R1 and R2 would be our customer sites and R3 would be the common ISP. Also, the link between R1 and R2 is considered "better" for routing purposes between inside networks than routing through the ISP.
Addressing Conventions
- subnet between routers X and Y is
10.XY.0.0/24with X having10.XY.0.Xand Y having10.XY.0.Y. - loopback address on X is
X.X.X.X/32 - ASN for router X is
6500X. - internal connected network for advertisement purposes on loopback on router X is
10.X.0.0/24
Backdoor routes
Lets start from a state where the internal networks (10.1.0.0/24 and 10.2.0.0/24) are advertised only in OSPF. The traffic will go as designed through the direct link R1-R2.
R1#show ip route ospf
10.0.0.0/8 is variably subnetted, 4 subnets, 2 masks
O 10.2.0.2/32 [110/11] via 10.12.0.2, 01:46:38, FastEthernet0/0
R2#show ip route ospf
10.0.0.0/24 is subnetted, 4 subnets
O 10.1.0.0 [110/11] via 10.12.0.1, 01:46:49, FastEthernet0/0
Now, we want to have redundancy through R3 so we also have to announce these prefixes through BGP into the ISP AS.
R3#show ip bgp
Network Next Hop Metric LocPrf Weight Path
*> 10.1.0.0/24 1.1.1.1 0 0 65001 i
*> 10.2.0.0/24 2.2.2.2 0 0 65002 i
And if we check the routing table on R1, we will see that the route towards 10.2.0.0/24 goes through BGP.
R1# show ip route
...
B 10.2.0.0 [20/0] via 3.3.3.3, 00:03:53
...
That happens because of the lower administrative distance of 20 for the eBGP route compared to the 110 of OSPF. This is where the backdoor routes come in: BGP allows us to increase this route's AD without having to touch the AD of the other routing protocols.
The get this result, simply add a network statement on R1 (the router that receives the prefix) with the "backdoor" keyword.
R1(config)# router bgp 65001
R1(config-router)# network 10.2.0.0 mask 255.255.255.0 backdoor
R1# show ip route
...
O 10.2.0.0 [110/11] via 10.12.0.2, 00:07:05, FastEthernet0/0
...
And by checking the BGP table we can see that the route is in RIB-failure, which means a better route already exists in the RIB.
R1#show ip bgp
BGP table version is 4, local router ID is 10.1.0.1
Status codes: s suppressed, d damped, h history, * valid, > best, i - internal,
r RIB-failure, S Stale
Origin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path
*> 10.1.0.0/24 0.0.0.0 0 32768 i
r> 10.2.0.0/24 3.3.3.3 0 65003 65002 i
If we kill the OSPF route we can see how the BGP route looks now:
R1# show ip route
...
B 10.2.0.0 [200/0] via 3.3.3.3, 00:00:27
...
This only solves one side of the problem. Remember that we wanted traffic between the internal networks to go through the OSPF route, but right now we have asymmetric routing: from R1 traffic is going directly to R2, but the return packets will go though the BGP route (R3). We need to declare the 10.1.0.0/24 as backdoor on R2 as well: R2(config-router)# network 10.1.0.0 mask 255.255.255.0 backdoor
Wrapping up
There are a few important points to make here about where and how this command should be used:
- this command needs to be used on the router which receives the prefix through BGP - so for
10.2.0.0/24which is originated by R2, the command needs to be configured on R1. - the effect it has is that it increases the AD of the BGP route from 20 to 200 (as a local route), making it less desirable than any other IGP route.
- it will also NOT advertise this network through BGP, which would be the normal effect of the network command without the backdoor keyword.
- remember to configure it on all sides that need to benefit from this routing path - that is on the side of the source AND the destination.